website/docs: RBAC docs (#7191)
* draft rbac docs * tweaks * add a permissions topic * tweaks * more changes * draft permissions topic * more content on roles * links * typo * more conceptual info * Optimised images with calibre/image-actions * more content on roles * add more x-ref links * fix links * more content * links * typos * polishing * Update website/docs/user-group-role/access-control/permissions.md Co-authored-by: Jens L. <jens@goauthentik.io> Signed-off-by: Tana M Berry <tanamarieberry@yahoo.com> * separwate conceptual vs procedural in permissions * finished groups procedurals * new page * added link * Update website/docs/user-group-role/access-control/permissions.md Co-authored-by: Jens L. <jens@goauthentik.io> Signed-off-by: Tana M Berry <tanamarieberry@yahoo.com> * polish * edits from PR review * restructured view section to remove repetition * rest of edits from PR review * polished flows and stages * polish * typo --------- Signed-off-by: Tana M Berry <tanamarieberry@yahoo.com> Co-authored-by: Tana Berry <tana@goauthentik.io> Co-authored-by: authentik-automation[bot] <135050075+authentik-automation[bot]@users.noreply.github.com> Co-authored-by: Jens L. <jens@goauthentik.io>
This commit is contained in:
parent
3f5d5e0408
commit
84fdd3c750
website
|
|
@ -66,7 +66,7 @@ return ak_is_group_member(request.user, name="test_group")
|
|||
|
||||
Fetch a user matching `**filters`.
|
||||
|
||||
Returns "None" if no user was found, otherwise returns the [User](/docs/user-group/user) object.
|
||||
Returns "None" if no user was found, otherwise returns the [User](/docs/user-group-role/user) object.
|
||||
|
||||
Example:
|
||||
|
||||
|
|
|
|||
|
|
@ -1,4 +1,4 @@
|
|||
- `user`: The current user. This may be `None` if there is no contextual user. See [User](../user-group/user/user_ref.md#object-properties).
|
||||
- `user`: The current user. This may be `None` if there is no contextual user. See [User](../user-group-role/user/user_ref.md#object-properties).
|
||||
|
||||
Example:
|
||||
|
||||
|
|
|
|||
|
|
@ -22,7 +22,7 @@ Keys prefixed with `goauthentik.io` are used internally by authentik and are sub
|
|||
|
||||
### Common keys
|
||||
|
||||
#### `pending_user` ([User object](../../user-group/user/user_ref.md#object-properties))
|
||||
#### `pending_user` ([User object](../../user-group-role/user/user_ref.md#object-properties))
|
||||
|
||||
`pending_user` is used by multiple stages. In the context of most flow executions, it represents the data of the user that is executing the flow. This value is not set automatically, it is set via the [Identification stage](../stages/identification/).
|
||||
|
||||
|
|
@ -110,9 +110,9 @@ Optionally overwrite the deny message shown, has a higher priority than the mess
|
|||
|
||||
#### User write stage
|
||||
|
||||
##### `groups` (List of [Group objects](../../user-group/group.md))
|
||||
##### `groups` (List of [Group objects](../../user-group-role/groups/index.mdx))
|
||||
|
||||
See [Group](../../user-group/group.md). If set in the flow context, the `pending_user` will be added to all the groups in this list.
|
||||
See [Group](../../user-group-role/groups/index.mdx). If set in the flow context, the `pending_user` will be added to all the groups in this list.
|
||||
|
||||
If set, this must be a list of group objects and not group names.
|
||||
|
||||
|
|
|
|||
|
|
@ -41,7 +41,7 @@ import Objects from "../expressions/_objects.md";
|
|||
|
||||
- `request`: A PolicyRequest object, which has the following properties:
|
||||
|
||||
- `request.user`: The current user, against which the policy is applied. See [User](../user-group/user/user_ref.md#object-properties)
|
||||
- `request.user`: The current user, against which the policy is applied. See [User](../user-group-role/user/user_ref.md#object-properties)
|
||||
|
||||
:::caution
|
||||
When a policy is executed in the context of a flow, this will be set to the user initiaing request, and will only be changed by a `user_login` stage. For that reason, using this value in authentication flow policies may not return the expected user. Use `context['pending_user']` instead; User Identification and other stages update this value during flow execution.
|
||||
|
|
@ -77,7 +77,7 @@ This includes the following:
|
|||
- `context['prompt_data']`: Data which has been saved from a prompt stage or an external source. (Optional)
|
||||
- `context['application']`: The application the user is in the process of authorizing. (Optional)
|
||||
- `context['source']`: The source the user is authenticating/enrolling with. (Optional)
|
||||
- `context['pending_user']`: The currently pending user, see [User](../user-group/user/user_ref.md#object-properties)
|
||||
- `context['pending_user']`: The currently pending user, see [User](../user-group-role/user/user_ref.md#object-properties)
|
||||
- `context['is_restored']`: Contains the flow token when the flow plan was restored from a link, for example the user clicked a link to a flow which was sent by an email stage. (Optional)
|
||||
- `context['auth_method']`: Authentication method (this value is set by password stages) (Optional)
|
||||
|
||||
|
|
|
|||
BIN
website/docs/user-group-role/access-control/flow-page.png
Normal file
BIN
website/docs/user-group-role/access-control/flow-page.png
Normal file
Binary file not shown.
|
After 
(image error) Size: 116 KiB |
16
website/docs/user-group-role/access-control/index.mdx
Normal file
16
website/docs/user-group-role/access-control/index.mdx
Normal file
|
|
@ -0,0 +1,16 @@
|
|||
---
|
||||
title: About access control
|
||||
---
|
||||
|
||||
import DocCardList from "@theme/DocCardList";
|
||||
import { useCurrentSidebarCategory } from "@docusaurus/theme-common";
|
||||
|
||||
To comply with important regulations such as PCI-DSS, HIPAA, SOC 2, and GDPR, it's necessary to have the ability to control which users have access to specific areas of the system, what [permissions](./permissions.md) they have globally and on certain objects, and a way to monitor [events](../../events) related to user activity.
|
||||
|
||||
In authentik, we provide role-based access control (RBAC), an industry standard for managing access control. By carefully designing roles with appropriate permissions, and then assigning those roles to groups, RBAC provides a fine-tuned approach to controlling user access.
|
||||
|
||||
RBAC is a way of ensuring the well-known [principal of least privilege](https://en.wikipedia.org/wiki/Principle_of_least_privilege) whereby "every module (such as a process, a user, or a program, depending on the subject) must be able to access only the information and resources that are necessary for its legitimate purpose."
|
||||
|
||||
To learn more about access control with authentik, refer to these topics:
|
||||
|
||||
<DocCardList items={useCurrentSidebarCategory().items} />
|
||||
|
|
@ -0,0 +1,118 @@
|
|||
---
|
||||
title: "Manage permissions"
|
||||
description: "Learn how to use global and object permissions in authentik."
|
||||
---
|
||||
|
||||
Refer to the following topics for instructions to view and manage permissions.
|
||||
|
||||
## View permissions
|
||||
|
||||
You can view all permissions that are assigned to a user, group, role, flow, or stage.
|
||||
|
||||
### View user, group, and role permissions
|
||||
|
||||
To view _object_ permissions for a specific user, role, or group:
|
||||
|
||||
1. Go to the Admin interface and navigate to **Directory**.
|
||||
2. Select either **Users**, **Groups**, or **Roles**
|
||||
3. Select a specific user/group/role by clicking on the name (this opens the details page).
|
||||
4. Click the **Assigned Permissions** tab at the top of the page (to the right of the **Permissions** tab).
|
||||
5. Scroll down to see both the global and object-level permissions.
|
||||
|
||||
:::info
|
||||
Note that groups do not have global permissions.
|
||||
:::
|
||||
|
||||
### View flow permissions
|
||||
|
||||
1. Go to the Admin interface and navigate to **Flows and Stages -> Flows**.
|
||||
2. Click the name of the flow (this opens the details page).
|
||||
3. Click the **Permissions** tab at the top of the page.
|
||||
4. View the assigned permissions using the **User Object Permissions** and the **Role Object Permissions** tabs.
|
||||
|
||||
### View stage permissions
|
||||
|
||||
1. Go to the Admin interface and navigate to **Flows and Stages -> Stagess**.
|
||||
2. On the row for the specific stage whose permissions you want to view, click the lock icon.
|
||||
3. On the **Update Permissions** tab, you can view the assigned permissions using the **User Object Permissions** and the **Role Object Permissions** tabs.
|
||||
|
||||
## Manage permissions
|
||||
|
||||
You can assign or remove permissions to a user, role, group, flow, or stage.
|
||||
|
||||
### Assign, modify, or remove permissions for a user
|
||||
|
||||
To assign or remove _object_ permissions for a specific user:
|
||||
|
||||
1. Go to the Admin interface and navigate to **Directory -> Users**.
|
||||
2. Select a specific user by clicking on the user's name.
|
||||
3. Click the **Permissions** tab at the top of the page.
|
||||
4. To assign or remove permissions that another _user_ has on this specific user:
|
||||
1. Click the **User Object Permissions** tab, click **Assign to new user**.
|
||||
2. In the **User** drop-down, select the user object.
|
||||
3. Use the toggles to set which permissions on that selected user object you want to grant to (or remove from) the specific user.
|
||||
4. Click **Assign** to save your settings and close the modal.
|
||||
5. To assign or remove permissions that another _role_ has on this specific user:
|
||||
Click the **Role Object Permissions** tab, click **Assign to new role**. 2. In the **User** drop-down, select the user object. 3. Use the toggles to set which permissions you want to grant to (or remove from) the selected role. 4. Click **Assign** to save your settings and close the modal.
|
||||
|
||||
To assign or remove _global_ permissions for a user:
|
||||
|
||||
1. Go to the Admin interface and navigate to **Directory -> Users**.
|
||||
2. Select a specific user the clicking on the user's name.
|
||||
3. Click the **Assigned Permissions** tab at the top of the page (to the right of the **Permissions** tab).
|
||||
4. In the **Assigned Global Permissions** area, click **Assign Permission**.
|
||||
5. In the **Assign permissions to user** modal, click the plus sign (**+**) and then click the checkbox beside each permission that you want to assign to the user. To remove permissions, deselect the checkbox.
|
||||
6. Click **Add**, and then click **Assign** to save your changes and close the modal.
|
||||
|
||||
### Assign or remove permissions on a specific group
|
||||
|
||||
:::info
|
||||
Note that groups themselves do not have permissions. Rather, users and roles have permissions assigned that allow them to create, modify, delete, etc., a group.
|
||||
Also there are no global permissions for groups.
|
||||
:::
|
||||
|
||||
To assign or remove _object_ permissions on a specific group by users and roles:
|
||||
|
||||
1. Go to the Admin interface and navigate to **Directory -> Groups**.
|
||||
2. Select a specific group by clicking the the group's name.
|
||||
3. Click the **Permissions** tab at the top of the page.
|
||||
To assign or remove permissions that another _user_ has on this specific group:
|
||||
1. Click the **User Object Permissions** tab, click **Assign to new user**.
|
||||
2. In the **User** drop-down, select the user object.
|
||||
3. Use the toggles to set which permissions on that selected group you want to grant to (or remove from) the specific user.
|
||||
4. Click **Assign** to save your settings and close the modal.
|
||||
4. To assign or remove permissions that another _role_ has on this specific group:
|
||||
Click the **Role Object Permissions** tab, click **Assign to new role**. 2. In the **Role** drop-down, select the role. 3. Use the toggles to set which permissions you want to grant to (or remove from ) the selected role. 4. Click **Assign** to save your settings and close the modal.
|
||||
|
||||
### Assign or remove permissions for a specific role
|
||||
|
||||
To assign or remove _object_ permissions for a specific role:
|
||||
|
||||
1. Go to the Admin interface and navigate to **Directory -> Roles**.
|
||||
2. Select a specific role the clicking on the role's name.
|
||||
3. Click the **Permissions** tab at the top of the page.
|
||||
To assign or remove permissions that another _user_ has on this specific role: 1. Click the **User Object Permissions** tab, click **Assign to new user**. 2. In the **User** drop-down, select the user object. 3. Use the toggles to set which permissions on that role you want to grant to (or remove from) the selected user. 4. Click **Assign** to save your settings and close the modal.
|
||||
4. To assign or remove permissions that another _role_ has on this specific group:
|
||||
Click the **Role Object Permissions** tab, click **Assign to new role**. 2. In the **Role** drop-down, select the role. 3. Use the toggles to set which permissions you want to grant to (or remove from) the selected role. 4. Click **Assign** to save your settings and close the modal.
|
||||
|
||||
To assign or remove _global_ permissions for a role:
|
||||
|
||||
1. Go to the Admin interface and navigate to **Directory -> Roles**.
|
||||
2. Select a specific role by clicking on the role's name.
|
||||
3. The **Overview** tab at the top of the page displays all assigned global permissions for the role.
|
||||
4. In the **Assigned Global Permissions** area, click **Assign Permission**.
|
||||
5. In the **Assign permissions to role** modal, click the plus sign (**+**) and then click the checkbox beside each permission that you want to assign to the role. To remove permissions, deselect the checkbox.
|
||||
6. Click **Assign** to save your changes and close the modal.
|
||||
|
||||
### Assign or remove flow permissions
|
||||
|
||||
1. Go to the Admin interface and navigate to **Flows and Stages -> Flows**.
|
||||
2. Click the name of the flow (this opens the details page).
|
||||
3. Click the **Permissions** tab at the top of the page.
|
||||
4. Add or remove permissions using the **User Object Permissions** and the **Role Object Permissions** tabs.
|
||||
|
||||
### Assign or remove stage permissions
|
||||
|
||||
1. Go to the Admin interface and navigate to **Flows and Stages -> Stagess**.
|
||||
2. On the row for the specific stage that you want to manage permissions, click the lock icon.
|
||||
3. On the **Update Permissions** tab, you can add or remove the assigned permissions using the **User Object Permissions** and the **Role Object Permissions** tabs.
|
||||
44
website/docs/user-group-role/access-control/permissions.md
Normal file
44
website/docs/user-group-role/access-control/permissions.md
Normal file
|
|
@ -0,0 +1,44 @@
|
|||
---
|
||||
title: "About permissions"
|
||||
description: "Learn about global and object permissions in authentik."
|
||||
---
|
||||
|
||||
Permissions are the central components in all access control systems, the lowest-level components, the controlling pieces of access data. Permissions are assigned to (or removed from!) to define exactly WHO can do WHAT to WHICH part of the overall software system.
|
||||
|
||||
:::info
|
||||
Note that global and object permissions only apply to objects within authentik, and not to who can access certain applications (which are access-controlled using [policies](../../policies/index.md).
|
||||
:::
|
||||
|
||||
## Fundamentals of authentik permissions
|
||||
|
||||
There are two main types of permissions in authentik:
|
||||
|
||||
- [**Global permissions**](#global-permissions)
|
||||
- [**Object permissions**](#object-permissions)
|
||||
|
||||
### Global permissions
|
||||
|
||||
Global permissions define who can do what on a global level across the entire system. Some examples in authentik are the ability to add new [flows](../../flow/index.md) or to create a URL for users to recover their login credentials.
|
||||
|
||||
You can assign _global permissions_ to individual [users](../user/index.mdx) or to [roles](../roles/index.mdx). The most common and best practice is to assign permissions to roles.
|
||||
|
||||
### Object permissions
|
||||
|
||||
Object permissions have two categories:
|
||||
|
||||
- **_User_ object permissions**: defines WHO (which user) can change the **_object_**
|
||||
- **_Role_ object permissions**: defines which ROLE can change the **_object_**
|
||||
|
||||
Object permissions are assigned, as the name indicates, to an object (users, [groups](../groups/index.mdx), roles, flows, and stages), and the assigned permissions state exactly what a user or role can do TO the object (i.e. what permissions does the user or role have on that object).
|
||||
|
||||
When working with object permissions, it is important to understand that when you are viewing the page for an object the permissions table shows which users or roles have permissions ON that object. Those permissions describe what those users or roles can do TO the object detailed on the page.
|
||||
|
||||
For example, the UI below shows a user page for the user named Peter.
|
||||
|
||||

|
||||
|
||||
You can see in the **User Object Permissions** table that another user, roberto, has permissions on Peter (that is, on the user object Peter).
|
||||
|
||||
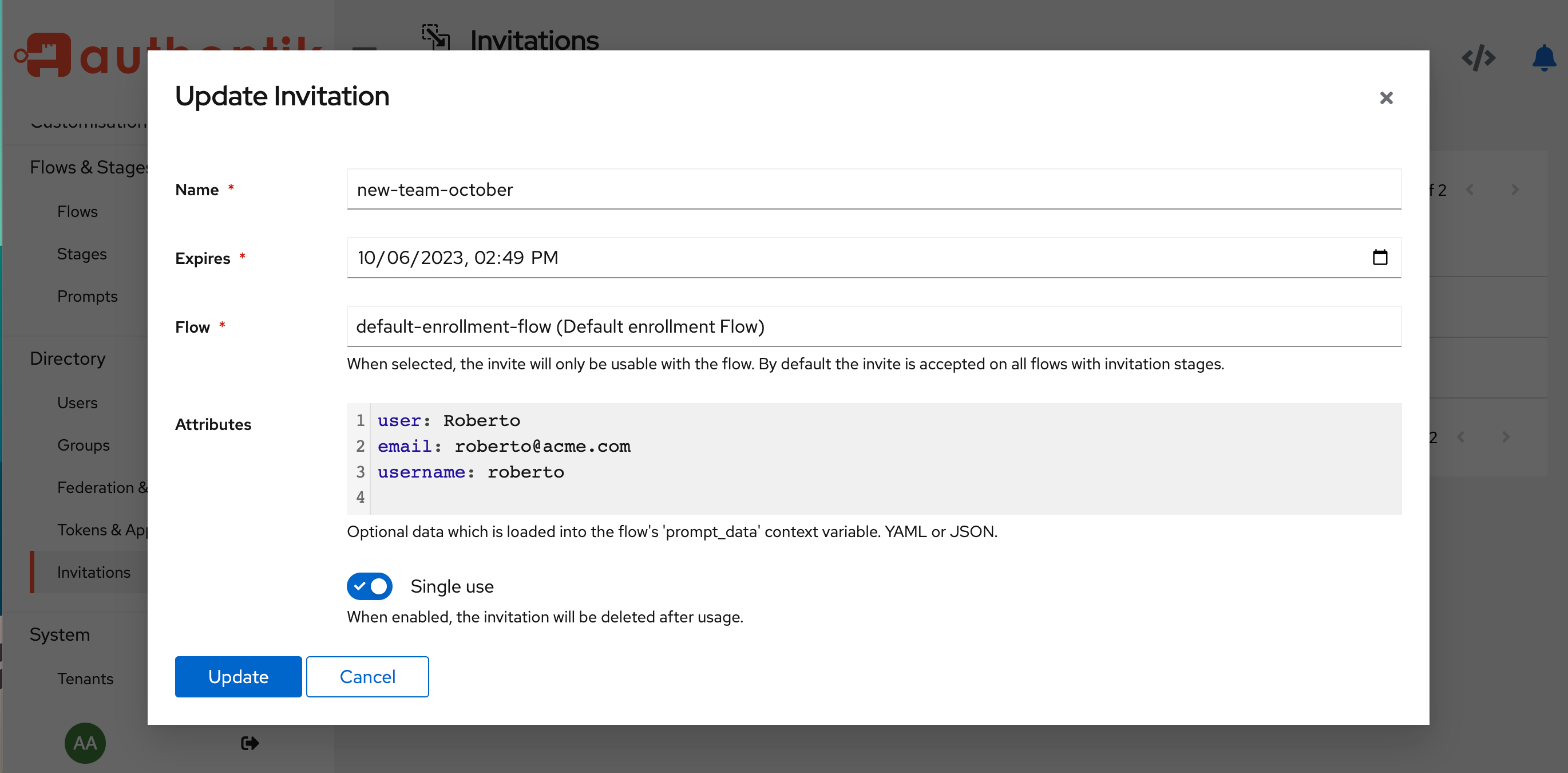
Looking at another example, with a flow object called `default-recovery-flow` you can see that the Admin user (akadmin) has all object permissions on the flow, but roberto only has a few permissions on that flow.
|
||||
|
||||

|
||||
BIN
website/docs/user-group-role/access-control/user-page.png
Normal file
BIN
website/docs/user-group-role/access-control/user-page.png
Normal file
Binary file not shown.
|
After 
(image error) Size: 119 KiB |
|
|
@ -1,5 +1,6 @@
|
|||
---
|
||||
title: Group
|
||||
title: About groups
|
||||
description: Learn about groups in authentik
|
||||
---
|
||||
|
||||
## Hierarchy
|
||||
45
website/docs/user-group-role/groups/manage_groups.md
Normal file
45
website/docs/user-group-role/groups/manage_groups.md
Normal file
|
|
@ -0,0 +1,45 @@
|
|||
---
|
||||
title: Manage groups
|
||||
description: "Learn how to work with groups in authentik."
|
||||
---
|
||||
|
||||
A group is a collection of users. Refer to the following sections to learn how to create and manage groups, assign users and roles to groups, and how [permissions](../access-control/manage_permissions.md) work on a group level.
|
||||
|
||||
## Create a group
|
||||
|
||||
To create a new group, follow these steps:
|
||||
|
||||
1. In the Admin interface, navigate to **Directory > Groups**.
|
||||
2. Click **Create** at the top of the Groups page.
|
||||
3. In the Create modal, define the following:
|
||||
- name of the group
|
||||
- whether or not users in that group will all be superusers (means anyone in that group has all permissions on everything)
|
||||
- the parent group
|
||||
- any custom attributes
|
||||
4. Click **Create**.
|
||||
|
||||
## Modify a group
|
||||
|
||||
To edit the group's name, parent group, whether or not the group is for superusers, associated roles, and any custom attributes, click the Edit icon beside the role's name. Make the changes, and then click **Update**.
|
||||
|
||||
To [add or remove users](../user/user_basic_operations.md#add-a-user-to-a-group) from the group, or to manage permissions assigned to the group, click on the name of the group to go to the group's detail page.
|
||||
|
||||
For more information about permissions, refer to ["Assign or remove permissions for a specific group"](../access-control/manage_permissions.md#assign-or-remove-permissions-for-a-specific-group).
|
||||
|
||||
## Delete a group
|
||||
|
||||
To delete a group, follow these steps:
|
||||
|
||||
1. In the Admin interface, navigate to **Directory > Groups**.
|
||||
2. Select the checkbox beside the name of the group that you want to delete.
|
||||
3. Click **Delete**.
|
||||
|
||||
## Assign, modify, or remove permissions for a group
|
||||
|
||||
You can grant a group specific global or object-level permissions. Any user who is a member of a group inherits all of the group's permissions.
|
||||
|
||||
For more information, review ["Permissions"](../access-control/permissions.md).
|
||||
|
||||
## Assign a role to a group
|
||||
|
||||
You can assign a role to a group, and then all users in the group inherit the permissions assigned to that role. For instructions and more information, see ["Assign a role to a group"](../roles/manage_roles.md#assign-a-role-to-a-group).
|
||||
20
website/docs/user-group-role/roles/index.mdx
Normal file
20
website/docs/user-group-role/roles/index.mdx
Normal file
|
|
@ -0,0 +1,20 @@
|
|||
---
|
||||
title: About roles
|
||||
---
|
||||
|
||||
import DocCardList from "@theme/DocCardList";
|
||||
import { useCurrentSidebarCategory } from "@docusaurus/theme-common";
|
||||
|
||||
Roles are a way to simplify the assignment of permissions. Roles are also the backbone of role-based access control (RBAC), an industry standard for managing [access control](../access-control). In authentik, RBAC is how you manage access to system components and specific objects such as flows, stages, users, etc.
|
||||
|
||||
Think of roles as a collection of permissions. A role, along with its "bucket" of assigned permissions, can then be assigned to a group, which means that every user who is a part of that group will inherit all of the permissions in that role's "bucket".
|
||||
|
||||
For example, let's take a look at the following scenario:
|
||||
|
||||
> You need to add 5 new users, all new hires, to authentik, your identity management system. These users will be the first team members on the brand new Security team, so they will need some high-level permissions, with object permissions to create and remove other users, revoke permissions, and send recovery emails. They will also need [global permissions](../access-control/permissions#fundamentals-of-authentik-permissions) to control access to flows and stages.
|
||||
|
||||
The easiest workflow for setting up these new users involves [creating a role](./manage_roles.md#create-a-role) specifically for their type of work, and then [assigning that role to a group](./manage_roles.md#assign-a-role-to-a-group) to which all of the users belong.
|
||||
|
||||
To learn more about working with roles in authentik, refer to the following topics:
|
||||
|
||||
<DocCardList items={useCurrentSidebarCategory().items} />
|
||||
48
website/docs/user-group-role/roles/manage_roles.md
Normal file
48
website/docs/user-group-role/roles/manage_roles.md
Normal file
|
|
@ -0,0 +1,48 @@
|
|||
---
|
||||
title: "Manage roles"
|
||||
description: "Learn how to work with roles and permissions in authentik."
|
||||
---
|
||||
|
||||
Roles are a collection of permissions, which can then be assigned, en masse, to a group. Using roles is a way to quickly grant permissions; by adding a user to the group with the appropriate assigned roles, any user in that group then inherits all of those permissions that are assigned to the role.
|
||||
|
||||
:::info
|
||||
In authentik, we assign roles to groups, not to individual users.
|
||||
:::
|
||||
|
||||
## Create a role
|
||||
|
||||
To create a new role, follow these steps:
|
||||
|
||||
1. In the Admin interface, navigate to **Directory > Roles**.
|
||||
2. Click **Create**, enter the name of the role, and then click **Create** in the modal.
|
||||
3. Next, [assign permissions to the role](../access-control/permissions.md#assign-or-remove-permissions-for-a-specific-role).
|
||||
|
||||
## Modify a role
|
||||
|
||||
To modify a role, follow these steps:
|
||||
|
||||
- To edit the name of the role, click the Edit icon beside the role's name.
|
||||
|
||||
- To modify the permissions that are assigned to the role click on the role's name to go to the role's detail page. There you can add, modify, or remove permissions. For more information, refer to ["Assign or remove permissions for a specific role"](../access-control/permissions.md#assign-or-remove-permissions-for-a-specific-role).
|
||||
|
||||
## Delete a role
|
||||
|
||||
To delete a role, follow these steps:
|
||||
|
||||
1. In the Admin interface, navigate to **Directory > Roles**.
|
||||
2. Select the checkbox beside the name of the role that you want to delete.
|
||||
3. Click **Delete**.
|
||||
|
||||
## Assign a role to a group
|
||||
|
||||
In authentik, roles are assigned to [groups](../groups/index.mdx), not to individual users.
|
||||
|
||||
1. To assign the role to a group, navigate to **Directory -> Groups**.
|
||||
2. Click the name of the group to which you want to add a role.
|
||||
3. On the group's detail page, on the Overview tab, click **Edit** in the **Group Info** area.
|
||||
4. On the **Update Group** modal, in the **Roles** field, scroll through the list of existent roles, and click to select the one you want to add to the group. (You can select multiple roles at once by holding the Control and Command keys while selecting the roles.)
|
||||
5. Click **Update** to add the role(s) and close the modal.
|
||||
|
||||
:::info
|
||||
To remove a role from a group, hold the Command key and click the name of the role that you want to remove from the group. This desepcts the role. Then click **Update**.
|
||||
:::
|
||||
|
Before 
(image error) Size: 171 KiB After 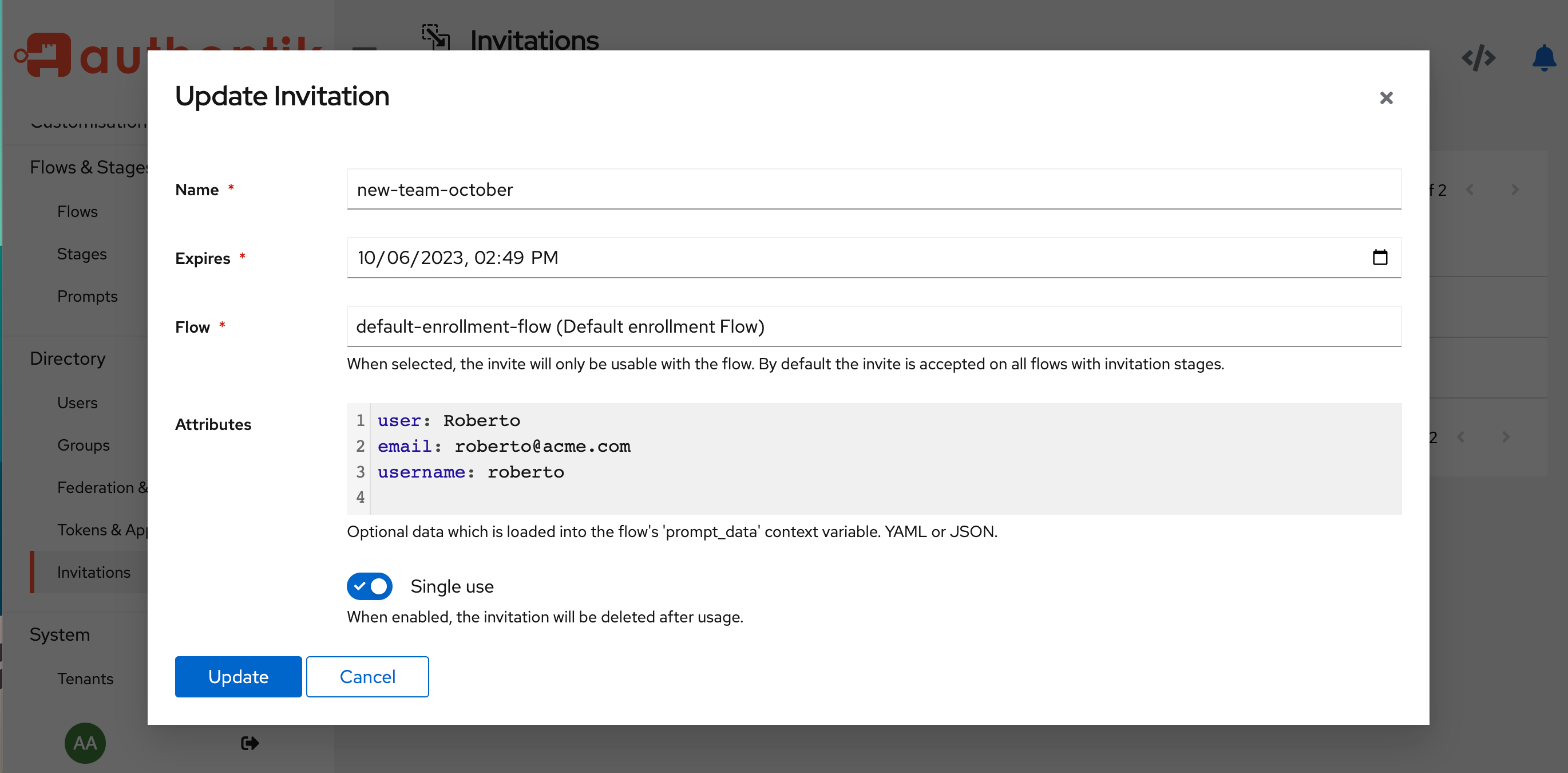
(image error) Size: 171 KiB 
|
|
|
@ -9,11 +9,8 @@ The following topics are for the basic management of users: how to create, modif
|
|||
> If you want to automate user creation, you can do that either by [invitations](./invitations.md), [`user_write` stage](../../flow/stages/user_write), or [using the API](/developer-docs/api/browser).
|
||||
|
||||
1. In the Admin interface of your authentik instance, select **Directory > Users** in the left side menu.
|
||||
|
||||
2. Select the folder where you want to create a user.
|
||||
|
||||
3. Click **Create** (for a default user).
|
||||
|
||||
4. Fill in the required fields:
|
||||
|
||||
- **Username**: This value must be unique across your user folders.
|
||||
|
|
@ -22,8 +19,8 @@ The following topics are for the basic management of users: how to create, modif
|
|||
5. Fill the **_optional_** fields if needed:
|
||||
|
||||
- **Name**: The display name of the user.
|
||||
- **Email**: The email address of the user. That will be used if there is a [notification rule](../../events/notifications) triggered or for [email stages](../../flow/stages/email).
|
||||
- **Is active**: Define is the newly created user account is active. Selected by default.
|
||||
- **Email**: The email address of the user. Email addresses are used in [email stages](../../flow/stages/email) and to receive [notifications](../../events/notifications), if configured.
|
||||
- **Is active**: Define if the newly created user account is active. Selected by default.
|
||||
- **Attributes**: Custom attributes definition for the user, in YAML or JSON format. These attributes can be used to enforce additional prompts on authentication stages or define conditions to enforce specific policies if the current implementation does not fit your use case. The value is an empty dictionary by default.
|
||||
|
||||
6. Click **Create**
|
||||
|
|
@ -43,7 +40,7 @@ To view details about a specific user:
|
|||
2. To see further details, click any of the other tabs:
|
||||
|
||||
- **Session** shows the active sessions established by the user. If there is any need, you can clean up the connected devices for a user by selecting the device(s) and then clicking **Delete**. This forces the user to authenticate again on the deleted devices.
|
||||
- **Groups** allows you to manage the group membership of the user. You can find more details on [groups](../group).
|
||||
- **Groups** allows you to manage the group membership of the user. You can find more details on [groups](../groups/index.mdx).
|
||||
- **User events** displays all the events generated by the user during a session, such as login, logout, application authorisation, password reset, user info update, etc.
|
||||
- **Explicit consent** lists all the permissions the user has given explicitly to an application. Entries will only appear if the user is validating an [explicit consent flow in an OAuth2 provider](../../providers/oauth2/). If you want to delete the explicit consent (because the application is requiring new permissions, or the user has explicitly asked to reset his consent on third-party apps), select the applications and click **Delete**. The user will be asked to again give explicit consent to share information with the application.
|
||||
- **OAuth Refresh Tokens** lists all the OAuth tokens currently distributed. You can remove the tokens by selecting the applications and then clicking **Delete**.
|
||||
|
|
@ -53,32 +50,38 @@ To view details about a specific user:
|
|||
|
||||
After the creation of the user, you can edit any parameter defined during the creation.
|
||||
|
||||
To modify a user object, go to **Directory > Users**, and click the edit icon beside the name.
|
||||
To modify a user object, go to **Directory > Users**, and click the edit icon beside the name. You can also go into [user details](#view-user-details), and click **Edit**.
|
||||
|
||||
You can also go into [user details](#view-user-details), and click **Edit**.
|
||||
### Assign, modify, or remove permissions for a user
|
||||
|
||||
## User recovery
|
||||
You can grant a user specific global or object-level permissions. Alternatively, you can add a user to a group that has the appropriate permissions, and the user inherits all of the group's permissions.
|
||||
|
||||
For more information, review ["Permissions"](../access-control/permissions.md).
|
||||
|
||||
## Add a user to a group
|
||||
|
||||
1. To add a user to a group, navigate to **Directory > Users** to display all users.
|
||||
2. Click the name of the user to display the full user details page.
|
||||
3. Click the **Groups** tab, and then click either **Add to existing group** or **Add to new group**.
|
||||
|
||||
## User credentials recovery
|
||||
|
||||
If a user has lost their credentials, there are several options.
|
||||
|
||||
### Email them a recovery link
|
||||
|
||||
1. In the Admin interface, navigate to **Directory > Users** to display all users.
|
||||
|
||||
2. Either click the name of the user to display the full User details page, or click the chevron (the › symbol) beside their name to expand the toptions.
|
||||
|
||||
2. Either click the name of the user to display the full User details page, or click the chevron (the › symbol) beside their name to expand the options.
|
||||
3. To generate a recovery link, which you can then copy and paste into an email, click **View recovery link**.
|
||||
|
||||
A pop-up will appear on your browser with the link for you to copy and to send to the user.
|
||||
A pop-up will appear on your browser with the link for you to copy and to send to the user.
|
||||
|
||||
### Automate email to a user
|
||||
|
||||
You can use our automated email to send a link with the URL for the user to reset their password. This option will only work if you have properly [configured a SMTP server during the installation](../../installation/docker-compose#email-configuration-optional-but-recommended) and set an email address for the user.
|
||||
|
||||
1. In the Admin interface, navigate to **Directory > Users** to display all users.
|
||||
|
||||
2. Either click the name of the user to display the full User details page, or click the chevron beside their name to expand the toptions.
|
||||
|
||||
3. To send the automated email to the user, click **Email recovery link**.
|
||||
|
||||
If the user does not receive the email, check if the mail server parameters [are properly configured](../../troubleshooting/emails).
|
||||
|
|
@ -88,9 +91,7 @@ If the user does not receive the email, check if the mail server parameters [are
|
|||
As an Admin, you can simply reset the password for the user.
|
||||
|
||||
1. In the Admin interface, navigate to **Directory > Users** to display all users.
|
||||
|
||||
2. Either click the name of the user to display the full User details page, or click the chevron beside their name to expand the toptions.
|
||||
|
||||
3. To reset the user's password, click **Reset password**, and then define the new value.
|
||||
|
||||
## Deactivate or Delete user
|
||||
|
|
@ -98,7 +99,6 @@ As an Admin, you can simply reset the password for the user.
|
|||
#### To deactivate a user:
|
||||
|
||||
1. Go into the user list or detail, and click **Deactivate**.
|
||||
|
||||
2. Review the changes and click **Update**.
|
||||
|
||||
The active sessions are revoked and the authentication of the user blocked. You can reactivate the account by following the same procedure.
|
||||
|
|
@ -111,7 +111,6 @@ You may instead deactivate the account to preserve identity data.
|
|||
:::
|
||||
|
||||
1. Go into the user list and select one (or multiple users) to delete and click **Delete** on the top-right of the page.
|
||||
|
||||
2. Review the changes and click **Delete**.
|
||||
|
||||
The user list refreshes and no longer displays the removed users.
|
||||
|
|
@ -43,7 +43,7 @@ elif ak_is_group_member(request.user, name="Minio users"):
|
|||
return None
|
||||
```
|
||||
|
||||
Note that you can assign multiple policies to a user by returning a list, and returning `None` will map no policies to the user, resulting in no access to the MinIO instance. For more information on writing expressions, see [Expressions](../../../docs/property-mappings/expression) and [User](../../../docs/user-group/user#object-attributes) docs.
|
||||
Note that you can assign multiple policies to a user by returning a list, and returning `None` will map no policies to the user, resulting in no access to the MinIO instance. For more information on writing expressions, see [Expressions](../../../docs/property-mappings/expression) and [User](../../../docs/user-group-role/user/user_ref#object-properties) docs.
|
||||
|
||||
### Creating application and provider
|
||||
|
||||
|
|
|
|||
|
|
@ -13,7 +13,7 @@ const docsSidebar = {
|
|||
{
|
||||
type: "category",
|
||||
label: "Installation",
|
||||
collapsed: false,
|
||||
collapsed: true,
|
||||
link: {
|
||||
type: "doc",
|
||||
id: "installation/index",
|
||||
|
|
@ -259,22 +259,51 @@ const docsSidebar = {
|
|||
},
|
||||
{
|
||||
type: "category",
|
||||
label: "Users & Groups",
|
||||
label: "Users, Groups, & Roles",
|
||||
items: [
|
||||
{
|
||||
type: "category",
|
||||
label: "Users",
|
||||
link: {
|
||||
type: "doc",
|
||||
id: "user-group/user/index",
|
||||
id: "user-group-role/user/index",
|
||||
},
|
||||
items: [
|
||||
"user-group/user/user_basic_operations",
|
||||
"user-group/user/user_ref",
|
||||
"user-group/user/invitations",
|
||||
"user-group-role/user/user_basic_operations",
|
||||
"user-group-role/user/user_ref",
|
||||
"user-group-role/user/invitations",
|
||||
],
|
||||
},
|
||||
{
|
||||
type: "category",
|
||||
label: "Groups",
|
||||
link: {
|
||||
type: "doc",
|
||||
id: "user-group-role/groups/index",
|
||||
},
|
||||
items: ["user-group-role/groups/manage_groups"],
|
||||
},
|
||||
{
|
||||
type: "category",
|
||||
label: "Roles",
|
||||
link: {
|
||||
type: "doc",
|
||||
id: "user-group-role/roles/index",
|
||||
},
|
||||
items: ["user-group-role/roles/manage_roles"],
|
||||
},
|
||||
{
|
||||
type: "category",
|
||||
label: "Access control",
|
||||
link: {
|
||||
type: "doc",
|
||||
id: "user-group-role/access-control/index",
|
||||
},
|
||||
items: [
|
||||
"user-group-role/access-control/permissions",
|
||||
"user-group-role/access-control/manage_permissions",
|
||||
],
|
||||
},
|
||||
"user-group/group",
|
||||
],
|
||||
},
|
||||
{
|
||||
|
|
|
|||
Reference in a new issue